
Healthcare API Security: OAuth 2.0, SMART Scopes, & HIPAA Compliance
One of the most significant shifts in modern healthcare is moving away from perimeter-based toward identity-based healthcare security. And this shift is driven by the rapid adoption of API-first architecture, seamless data flows, integrations with third-party apps, and cloud-based services.
In a perimeter-based system, the security approach was to trust everything inside the system, given all access, and external access was seen as a threat. However, in modern healthcare, this approach is no longer safe in an interconnected environment.
That’s why healthcare API security works on a Zero Trust policy, where nothing is trusted, and every request is authenticated, validated, and authorized. The reason for adopting this approach is that, in an API-driven ecosystem, every exposed entry point is a potential access point to sensitive patient data.
To eliminate this gap, modern healthcare API security depends on three measures:
- OAuth 2.0 for secure authentication
- SMART Scopes for deciding authorized, context-aware data scopes
- HIPAA Compliance for API regulatory safeguards
Most importantly, what healthcare organizations must remember is to maintain a balance between data liquidity and compliance. Although seamless data exchange is necessary for adapting to new technologies, protecting PHI and building compliant systems is non-negotiable.
In this guide, we will break down the core security risks and the best practices for implementing healthcare API security OAuth HIPAA strategies for ensuring compliance without compromising flexibility and scalability.
Core Security Risks in Healthcare APIs
Although the API-driven healthcare systems make data exchange faster, it also expands the attack surface. This is because every API endpoint is a potential entry point to access sensitive PHI. Here are some of the core security risks that may impact patient data security and privacy:
- Unauthorized Access & Token Misuse: This is the most common and dangerous risk if the access tokens are not handled properly. In OAuth 2.0-based systems, these tokens are keys to access sensitive patient data. If these tokens are not stored properly in browser storage, mobile apps, or are stored in non-encrypted or unvalidated forms, then they can be intercepted or reused by unauthorized users.
- Overexposed FHIR Endpoints: Another risk is the overexposed FHIR APIs. These APIs are designed for flexibility; this flexibility can expose patient data if the endpoints are not protected properly. If these are overexposed, then it can lead to access to the entire patient records and data is not restricted by context or role.
- Data Leakage During Transmission: One more risk is data leakage during data transmission if there is no end-to-end encryption for data pathways. Moreover, if there is a weak TLS configuration and improper certificate validation, it may lead to possible interpretation of PHI in transit or man-in-the-middle (MITM) attacks. So, in healthcare, even a single exposed API can mean a reportable breach.
- Compliance Risks (HIPAA Violations): When the APIs are implemented, they do not automatically align with compliance. However, there are some common gaps where compliance risks occur, such as no audit logging of API access, lack of role-based access control, and over-permissioned systems. That’s why it is important to manage HIPAA compliance, which needs an auditable, unauthorized exposure trigger for accountability.
This is why implementing healthcare API security is important for building secure, scalable, and interoperable healthcare systems. Let’s understand how security frameworks such as OAuth 2.0, SMART on FHIR scopes, and HIPAA compliance work.
Healthcare API Security Starter Kit: OAuth 2.0 Implementation Checklist
DownloadThe Authentication Gold Standard: OAuth 2.0 for Healthcare
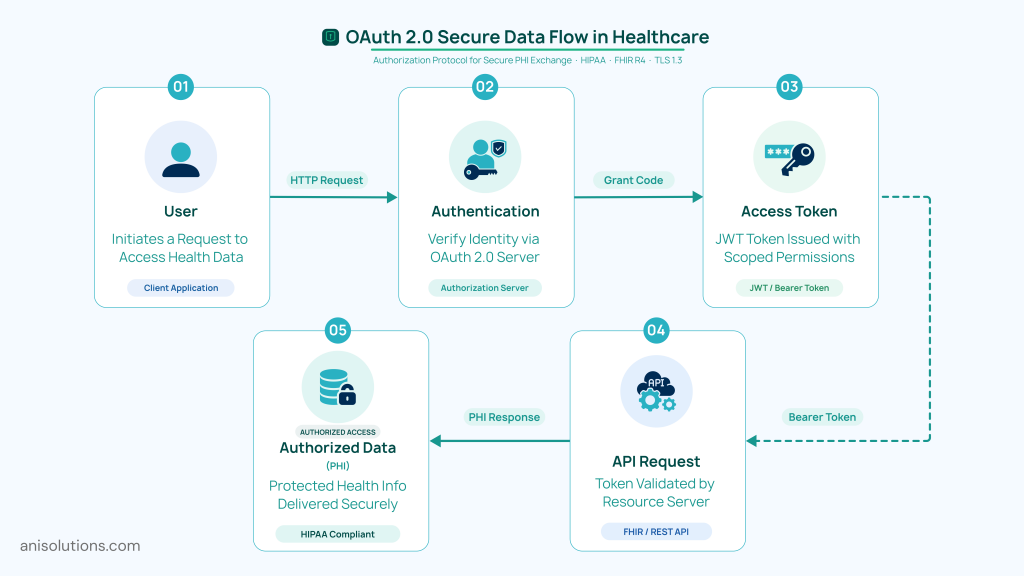
With healthcare systems adopting API-driven architecture, securing healthcare APIs with OAuth 2.0 becomes essential. The OAuth 2.0 for healthcare authenticates and authorizes access to patient data, controlling who can access sensitive PHI.
Moreover, the OAuth 2.0 enables access to sensitive PHI without compromising user credentials. Rather than sharing usernames and passwords every time, it authenticates users through an Identity Provider (IdP). These IdPs issue secure access tokens for requesting data from APIs, ensuring the access to patient data is controlled and traceable.
There are three types of OAuth tokens: access tokens for short-term access to APIs. Then there are refresh tokens, which allow renewal of access securely without needing to reauthenticate.
Finally, the identity providers (IdPs) verify identity and manage authentication workflows, ensuring that the right person is accessing the data. More importantly, OpenID Connect and OAuth 2.0 are different, as OpenID Connect provides an identity layer to confirm the identity of a user, whereas OAuth 2.0 authorizes the data allowed to be accessed by that identity or role.
When implemented correctly, the OAuth 2.0 ensures that both patient-to-provider and system-to-system data exchange remains secure, without compromising interoperability.
Authorization Precision: Implementing SMART Scopes for FHIR
OAuth 2.0 sets the foundation for who can access the data in the system, whereas SMART scopes define what data is accessed specifically. With SMART on FHIR, secure healthcare organizations enable context-aware and precise access control and extend OAuth 2.0 protection.
SMART scopes define access using a structured and clear format, and the format looks like context/resource.permission. To give you an example, the format patient/Observation.read allows only an application to read clinical observations, such as lab results or vitals, for a specific patient. Whereas, user/Patient.write enables the provider to update patient records based on their role.
With this, healthcare organizations can control the data access at a granular level, and it is essential for healthcare environments, where unrestricted access can lead to compliance violations. This is where SMART scopes ensure that third-party applications only access the minimum necessary data, aligning directly with HIPAA compliance for API.
Another advantage of the SMART on FHIR scope is context-based authorization, which helps in restricting access based on patient context, user context, and system context. By embedding SMART scopes, healthcare organizations can reduce the risk of overexposure and unauthorized data access.
Most importantly, when it is combined with OAuth 2.0, it creates a robust authorization layer ensuring healthcare data is shared securely, efficiently, and in compliance with regulatory standards.
FHIR API HIPAA Compliance Checklist (Audit-Ready Framework)/p> Get Now
HIPAA Compliance for FHIR APIs
With the increased adoption of FHIR APIs, the need for HIPAA compliance for APIs is becoming crucial. While HIPAA compliance does not mention APIs or FHIR standards explicitly, any system that creates, transmits, or stores PHI must comply with the HIPAA Security Rule.
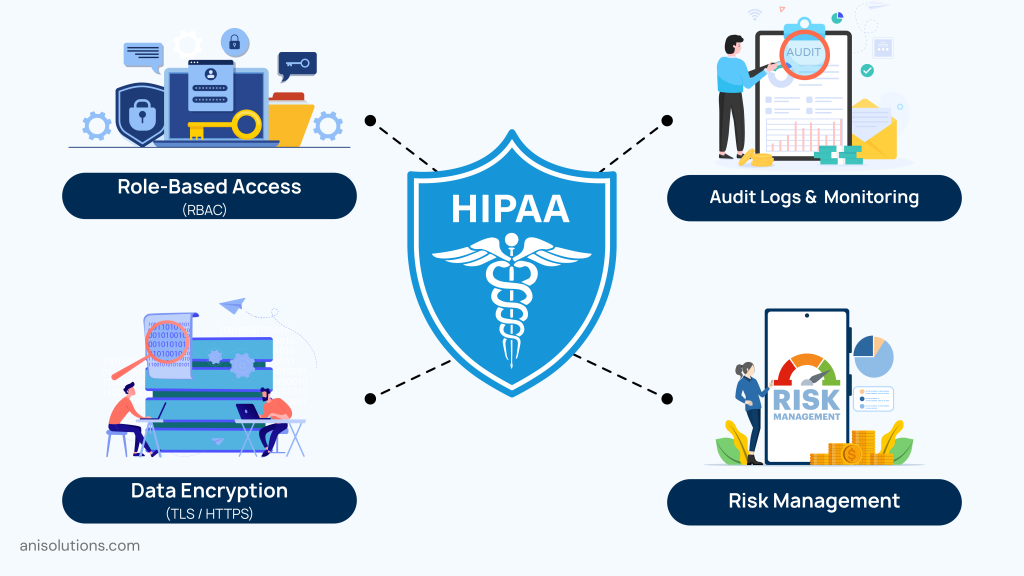
Here are the HIPAA compliance requirements for FHIR APIs that must be implemented for both administrative and technical security:
Administrative Safeguards
- Role-Based Access Control (RBAC): This ensures that only authorized users can access patient data and only data that is relevant to their role.
- Audit Logs & Monitoring: With this, it is possible to track who accessed what data, when, and from where, along with the changes made to the data.
- Risk Management: Under this requirement, the healthcare organizations must regularly evaluate vulnerabilities in API infrastructure and fix them on time.
Technical Safeguards
- Data Encryption: Healthcare organizations must end-to-end encrypt their data pathways to protect patient data in transit and at rest. They can use TLS/HTTPS to prevent interception in transmission and use secure cloud environments to protect data at rest.
- Access Control & Minimum Necessary Rule: It is important to restrict data access to a minimum and share only the data that is required by that role or patient. If the APIs are overexposed and give broad access scopes, then HIPAA compliance is violated, leading to penalties.
Audit & Accountability
- Breach Notification Requirements: If PHI is exposed through APIs, the healthcare organization must notify affected parties and report it within defined regulatory timelines.
- Business Associate Agreements (BAAs): Any third-party app or service accessing PHI via APIs must sign a BAA to ensure shared responsibility for data protection.
In short, HIPAA compliance in API ecosystems is not just about securing infrastructure; it’s about enforcing accountability, traceability, and least-privilege access across every connected system.
Advanced Security Best Practices for Healthcare APIs
Implementing foundational standards such as OAuth 2.0, SMART scope, and HIPAA compliance is essential; it is not sufficient to protect data from all angles. To truly secure modern healthcare systems, organizations must adopt advanced,proactive measures that address evolving threats in API-driven environments.
Here are some of the advanced healthcare API security measures that extend the foundational standards:
- API Gateway & Rate Limiting: An API gateway protects patient data by managing and filtering incoming traffic. Moreover, rate limiting helps in preventing abuse, such as excessive requests or denial-of-service (DoS) attacks, ensuring system stability and controlled access to sensitive endpoints.
- Threat Detection & Anomaly Monitoring: With AI-driven monitoring tools, healthcare organizations can detect unusual API behavior and intercept any cyberattacks. For example, sudden spikes in data access or repeated requests across multiple patient records can indicate potential security threats, enabling faster response and mitigation.
- Token Lifecycle Management: Access tokens should be short-lived to reduce the risk of misuse. Secure refresh token mechanisms, token rotation, and revocation strategies are critical to maintaining control over session integrity and preventing unauthorized reuse.
- Avoiding Over-Scoping Access: Overly broad permissions remain one of the most common security gaps. Rather than granting complete or blanket access for instance patient/*.read, organizations should enforce granaulr SMART scopes allowing only minimum necessary access.
Healthcare API Security Assessment (Free Expert Review)
Access NowConclusion: Security as a Strategic Enabler
In a nutshell, healthcare ecosystems are moving towards API-driven architecture from their closed environment. This is why perimeter-based security is no longer viable, and a healthcare API security supported by OAuth 2.0, SMART scopes, and HIPAA compliance for APIs is essential.
With this approach, every endpoint is protected, and every request to access data is authenticated, authorized, and validated before granting access. However, continuous monitoring, audit readiness, and strict adherence to least-privilege access are essential to maintain long-term security.
So, if you want to stay connected securely, then embedding healthcare API security, OAuth, and HIPAA best practices is non-negotiable. At A&I Solutions, our developers and EHR integration experts have experience in implementing interoperability without compromising security, accountability, and scalability.
Ready to build interoperability that not just makes data flow faster but also secure? Then talk to our experts and get started with system assessment.
Frequently Asked Questions
OAuth 2.0 is an authorization framework that allows applications to access specific healthcare resources using access tokens, without exposing user credentials. OpenID Connect (OIDC) extends OAuth by adding an authentication layer, issuing ID tokens that verify the user’s identity. In healthcare systems, OAuth controls access to APIs, while OIDC ensures the user’s or provider’s identity is properly validated.
SMART scopes for FHIR prevent data scraping by enforcing fine-grained, context-aware access control. Instead of granting broad access, scopes limit applications to specific data types and patient contexts, such as allowing access only to a single patient’s observations. This ensures that apps cannot extract large datasets, aligning with the minimum necessary rule and significantly reducing the risk of bulk data exposure.
HIPAA requires systems handling protected health information to maintain detailed audit controls. For FHIR APIs, this means logging every access event, including who accessed the data, what data was accessed, when the access occurred, and from where. These logs must be secure, tamper-resistant, and retained for compliance audits, breach investigations, and regulatory reporting.
Healthcare data encryption protects information during transmission and storage, but it does not control who is allowed to access that data. Without a robust Identity Provider (IdP), unauthorized users may still gain access through compromised credentials or weak authentication mechanisms. An IdP ensures proper identity verification, token issuance, and access control, making it essential for enforcing Zero Trust security in healthcare APIs.
Healthcare API security audits commonly reveal issues such as overly broad access permissions, weak or improperly validated tokens, missing or incomplete audit logs, and insecure storage of access credentials. Many systems also lack rate limiting and anomaly detection, which increases the risk of unauthorized access and large-scale data exposure. These vulnerabilities often stem from misconfigured OAuth implementations and insufficient access control.
Managing token expiration in high-concurrency environments requires the use of short-lived access tokens combined with secure refresh token mechanisms. Systems should implement token caching with expiration tracking and enable silent token refresh to avoid disruptions. Centralized token validation and revocation capabilities are also important for maintaining security while ensuring seamless performance under high volumes of API requests.
An organization can achieve HIPAA compliance using third-party cloud gateways, provided the vendor meets all regulatory requirements. This includes signing a Business Associate Agreement (BAA), supporting encryption, access controls, and audit logging, and ensuring secure handling of protected health information. However, compliance remains a shared responsibility, and the healthcare organization is ultimately accountable for data protection.
The first step in securing healthcare APIs with OAuth 2.0 for a legacy backend is to introduce an authorization layer, typically through an API gateway or middleware. This allows token-based authentication and access control to be enforced without modifying the core system. It enables organizations to secure existing infrastructure while gradually transitioning toward a modern, API-first architecture.
- On April 15, 2026
- 0 Comment


