
How to Design Secure HIPAA-Compliant EHR Architecture
In 2025, the breaches of electronic Protected Health Information (ePHI) became increasingly frequent. According to HIPAA Journal reports, in September 2025, 41 incidents were recorded, with the highest number of cases occurring in April.
In most cases, the reason for these security risks is poorly designed, non-compliant EHR architecture, where security is integrated way too late in the development, rather than from day one. A modern EHR system has multiple architectural layers, from data storage and application logic to integrations and user access.
That’s why HIPAA-compliant EHR architecture design has become critical in 2026. Modern EHR systems must be built with security embedded across every layer—from data storage and access control to integrations and user interactions.
A truly secure EHR design goes beyond adding encryption or access controls later. It requires a structured approach to how ePHI is stored, accessed, transmitted, and monitored throughout the system lifecycle.
Understanding HIPAA architecture requirements ensures that your EHR remains compliant, audit-ready, and resilient—without compromising performance or scalability.
In this guide, we’ll break down how to design a HIPAA-compliant EHR architecture using a risk-based approach, so compliance becomes a natural outcome of your system design.
Step 1: Risk-Based Approach to HIPAA-Compliant EHR Architecture Design
Before designing the HIPAA-compliant architecture and deciding how data is stored, encrypted, or accessed, you need to understand the risks associated with it. You need answers to questions such as what kind of ePHI the system handles, where it flows, and who uses it.
These are the foundational questions that shape the security and compliance of the entire EHR system. The first step in the risk-driven approach is identifying the types of ePHI processed by EHR, including clinical notes, lab results, medication data, or patient-generated data. Each of these data types has a different sensitivity level and compliance needs. Without a proper classification system, it applies inconsistent protections, creating gaps in the system.
After this comes mapping how ePHI flows across the architecture, as patient data is always moving between application services, databases, and third-party integrations. If these data flows are not secured, then the chances of breaches and data loss increase with each data transmission through APIs, background jobs, or integration points.
Finally, it is important to define who needs access to ePHI and under what conditions. This decision drives the role-based access control, multi-factor authentication, and other access-control protection for the EHR system.
By identifying high-risk architectural zones early, teams can prevent compliance gaps that often surface during audits or after breaches. A risk-driven approach ensures HIPAA compliance is built into the system’s structure, not fixed after issues occur.
If you want to understand how architectural layers influence security, performance, and scalability at a broader level, read The Complete Guide to Understanding EHR Software Architecture.
Step 2: Data Segregation & Access Control in Secure EHR Design
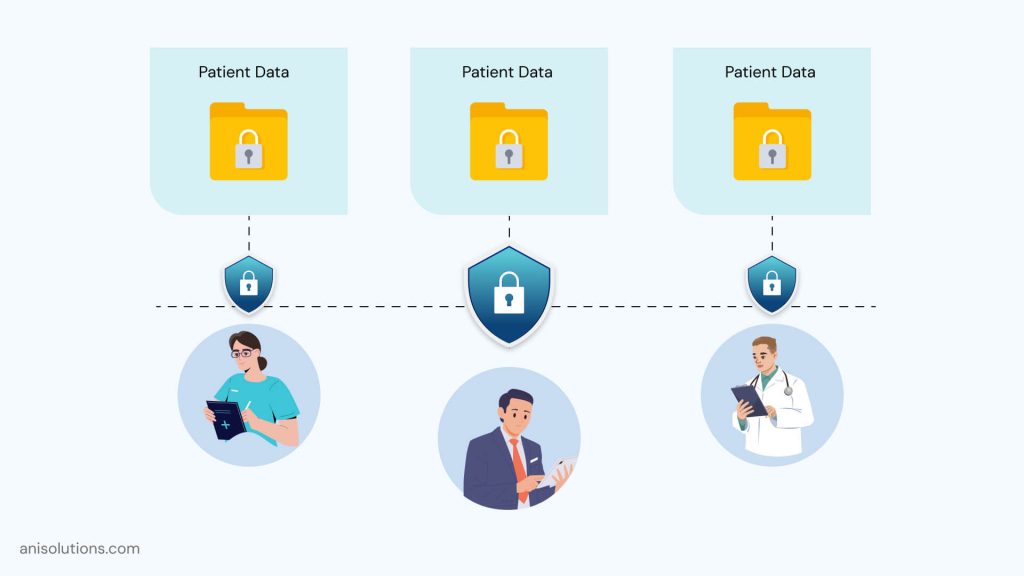
One of the most common reasons HIPAA violations is poor data segregation. An EHR system deals with operational, administrative, or system-level data— the risk of unintended data exposure increases significantly.
In a HIPAA-ready architecture, it is important to separate clinical data from non-clinical data, such as application logs, usage analytics, and operational metadata. Without this separation, sensitive data can get mixed in logs, error messages, or third-party observability, increasing the chances of compliance violations.
Similarly, enforcing access controls is also crucial. Not every service, background process, or staff member needs access to every data or sensitive ePHI. Architectural decisions must enforce least-privilege access by design, ensuring that only authorized services and users can access the protected data.
This segregation also supports auditability without increasing the attack surface. When ePHI access is tightly scoped, audit logs become clearer, investigations become faster, and compliance reporting becomes more reliable. At the same time, the system avoids broad access patterns that make breaches harder to detect and contain.
By designing clear data boundaries and access controls at the architecture level, healthcare organizations reduce accidental exposure, limit blast radius during incidents, and create a more secure, HIPAA-compliant EHR system from the ground up.
Step 3: Core HIPAA Architecture Requirements for EHR Systems
When it comes to security and compliance in EHR architecture, it cannot be added later; it needs to be embedded from the start. Certain controls must be architectural decisions, embedded into how the system is designed, how data flows, and how access is enforced.
When these controls are treated as configurations or optional add-ons, compliance gaps inevitably emerge. The table below outlines the non-negotiable security controls that must exist at the architecture level in a HIPAA-ready EHR system:
| Architectural Control | HIPAA Security Objective | Why It Must Be Architectural |
| Encryption at rest & in transit | Protect ePHI confidentiality | Must be enforced by storage, database, and network layers—not applications |
| Role-Based Access Control (RBAC) | Restrict unauthorized access | Requires centralized identity and permission modeling |
| Authentication & session control | Ensure access integrity | Impacts how users and services interact across the system |
| Tamper-resistant audit logging | Accountability and traceability | Logs must be part of core data flows, not external add-ons |
| Backup, retention, and recovery | Ensure data availability | Must align with system architecture and storage design |
While these controls are often discussed individually, their true effectiveness depends on how they are architected together. For example, encryption only works if key management is centralized and access-aware. RBAC fails if services bypass identity enforcement through direct database access. Audit logging becomes meaningless if it can be altered or selectively disabled.
Architectural security controls also support audit readiness by default. When access, encryption, and logging are built into the system’s core layers, compliance evidence is generated naturally through system operations, rather than manually assembled during audits.
By enforcing these controls at the architectural level, EHR systems move from reactive compliance to structural HIPAA alignment, reducing long-term risk and strengthening overall security.
Step 4: Using AI Within Secure and Compliant EHR Design

It’s true that AI can boost HIPAA compliance, but only when it is applied intentionally and architecturally, not as a bolt-on feature. In a HIPAA-compliant EHR, AI’s role is not to replace security controls or compliance processes, but to enhance visibility, detection, and response within an already secure system design.
One of the most effective uses of AI is in detecting unusual access patterns and anomalous behavior. In complex EHR environments, traditional rule-based monitoring often fails to catch subtle risks, such as inappropriate access by authorized users or abnormal service-to-service activity.
Moreover, AI models can analyze historical access patterns and flag decorations that may indicate compromised credentials, insider threats, or misconfigured permissions, without expanding access to ePHI.
AI can also support proactive identification of potential security incidents by correlating signals across audit logs, authentication events, and system activity. Instead of reacting after a breach occurs, security teams gain early warnings that allow faster investigation and containment, reducing compliance exposure.
However, AI must operate within strict architectural boundaries, with it only allowed to consume metadata, access logs, and behavioral signals, not raw clinical data, unless required. Outputs must remain explainable, traceable, and auditable, supporting HIPAA audit expectations rather than complicating them.
When designed correctly, AI becomes a compliance amplifier, improving monitoring and risk detection while preserving the core principles of least privilege, transparency, and accountability. In a HIPAA-compliant EHR architecture, AI strengthens security posture; it does not define it.
Step 5: Reference Model for HIPAA-Compliant EHR Architecture Design
After defining risks, data boundaries, and core security controls, the next step is translating those principles into a clear reference architecture. A HIPAA-compliant EHR architecture doesn’t need to be overly complex, but it must be intentional, layered, and robust by design.
At the center of the architecture is the application layer, which handles clinical workflows such as charting, orders, care coordination, and documentation. This layer should never access all patient data directly. Instead, it must be through controlled services that enforce identity checks, authorization rules, and audit logging at every request.
With this done, a centralized identity and access management (IAM) layer is critical. This layer governs user authentication, role-based access control, session handling, and service-to-service authorization. More specifically, centralization ensures consistent enforcement of least-privilege access across the entire system, rather than fragmented rules spread across applications.
All clinical data storage must be encrypted and isolated, with strict access paths defined through approved services only. Alongside storage, a dedicated audit logging and monitoring pipeline captures access events, data changes, and security signals in a tamper-resistant manner, supporting both real-time monitoring and HIPAA audit requirements.
Equally important are backup, recovery, and availability mechanisms for the safeguarding of data and functionality. So, the final goal is to build a repeatable and defensible architecture, not a perfect one.
When security, access, and compliance controls are embedded into each architectural layer, HIPAA compliance becomes a natural outcome of system design, not an ongoing firefight as the EHR scales and evolves.
Final Take: Designing Secure, HIPAA-Compliant EHR Architecture
Long story short, when you keep compliance at the forefront of EHR software architecture, it reduces long-term risks. With HIPAA-compliant EHR architecture, security and compliance are embedded into the system by design rather than added later.
More importantly, data access is tightly controlled, ePHI flows are clearly defined, and audit readiness becomes a natural outcome of daily system operations. This approach not only lowers the likelihood of breaches and failed audits but also reduces maintenance overhead as the system evolves.
Ultimately, compliance-first architecture creates EHR platforms that are more secure, scalable, and trusted by both providers and patients. So, if you want to build a secure and compliant EHR, then Click here to book your free demo.
Frequently Asked Questions
Q. Do I need a separate Business Associate Agreement (BAA) for integrated AI models or third-party LLMs used within an EHR system?
Yes, if an AI vendor or LLM provider creates, receives, processes, or stores PHI on your behalf, a separate BAA is required. Without it, using the AI service introduces direct HIPAA compliance and liability risks.
Q. How can AI-powered EHR architecture prevent re-identification when using de-identified datasets for model training?
Prevent re-identification by enforcing strict data minimization, removing indirect identifiers, isolating training environments, restricting cross-dataset access, and applying architectural controls that block reverse linkage between training data and live clinical systems.
Q. How do you architect an audit trail for decisions made by an AI agent instead of a human user?
AI decisions must generate audit logs equivalent to human actions, capturing input data references, model version, decision output, timestamps, and execution context—stored immutably to ensure traceability, explainability, and HIPAA audit readiness.
Q. Can AI agents automatically redact PHI from clinical notes before data is stored or transmitted to auxiliary systems?
Yes, but redaction must occur within a controlled, HIPAA-compliant processing layer. The architecture should ensure raw PHI never reaches downstream systems, logs, or analytics tools before redaction is completed and validated.
Q. How does a Zero-Trust EHR architecture manage AI’s need for high-volume or continuous data access?
Zero-Trust architecture limits AI access through scoped service identities, short-lived credentials, purpose-bound permissions, and monitored data pipelines—allowing necessary volume while preventing unrestricted or persistent access to ePHI.
Q. Is data processed or cached inside AI gateways considered PHI, and how should it be secured architecturally?
Yes, if cached or processed data contains identifiers or clinical context, it is PHI. Architecturally, it must be encrypted, access-controlled, logged, time-limited, and isolated to meet HIPAA security requirements.
Yes, if an AI vendor or LLM provider creates, receives, processes, or stores PHI on your behalf, a separate BAA is required. Without it, using the AI service introduces direct HIPAA compliance and liability risks.
Prevent re-identification by enforcing strict data minimization, removing indirect identifiers, isolating training environments, restricting cross-dataset access, and applying architectural controls that block reverse linkage between training data and live clinical systems.
AI decisions must generate audit logs equivalent to human actions, capturing input data references, model version, decision output, timestamps, and execution context—stored immutably to ensure traceability, explainability, and HIPAA audit readiness.
Yes, but redaction must occur within a controlled, HIPAA-compliant processing layer. The architecture should ensure raw PHI never reaches downstream systems, logs, or analytics tools before redaction is completed and validated.
Zero-Trust architecture limits AI access through scoped service identities, short-lived credentials, purpose-bound permissions, and monitored data pipelines—allowing necessary volume while preventing unrestricted or persistent access to ePHI.
Yes, if cached or processed data contains identifiers or clinical context, it is PHI. Architecturally, it must be encrypted, access-controlled, logged, time-limited, and isolated to meet HIPAA security requirements.
- On February 2, 2026
- 0 Comment


